HTTP/S MHDDOS GET is an HTTP flood designed to overwhelm web servers’ resources by continuously requesting single or multiple URLs from many source attacking machines.
HTTP/S MHDDOS GET is an HTTP flood attack based on the MHDDOS attack tool. MHDDOS contains multiple attack vectors designed to bypass various DDoS mitigation types.
HTTP/S MHDDOS GET generates GET requests. The attack uses a large pool of user agents and referrers. When the servers’ limits of concurrent connections are reached, the server can no longer respond to legitimate requests from other users.
Technical Analysis
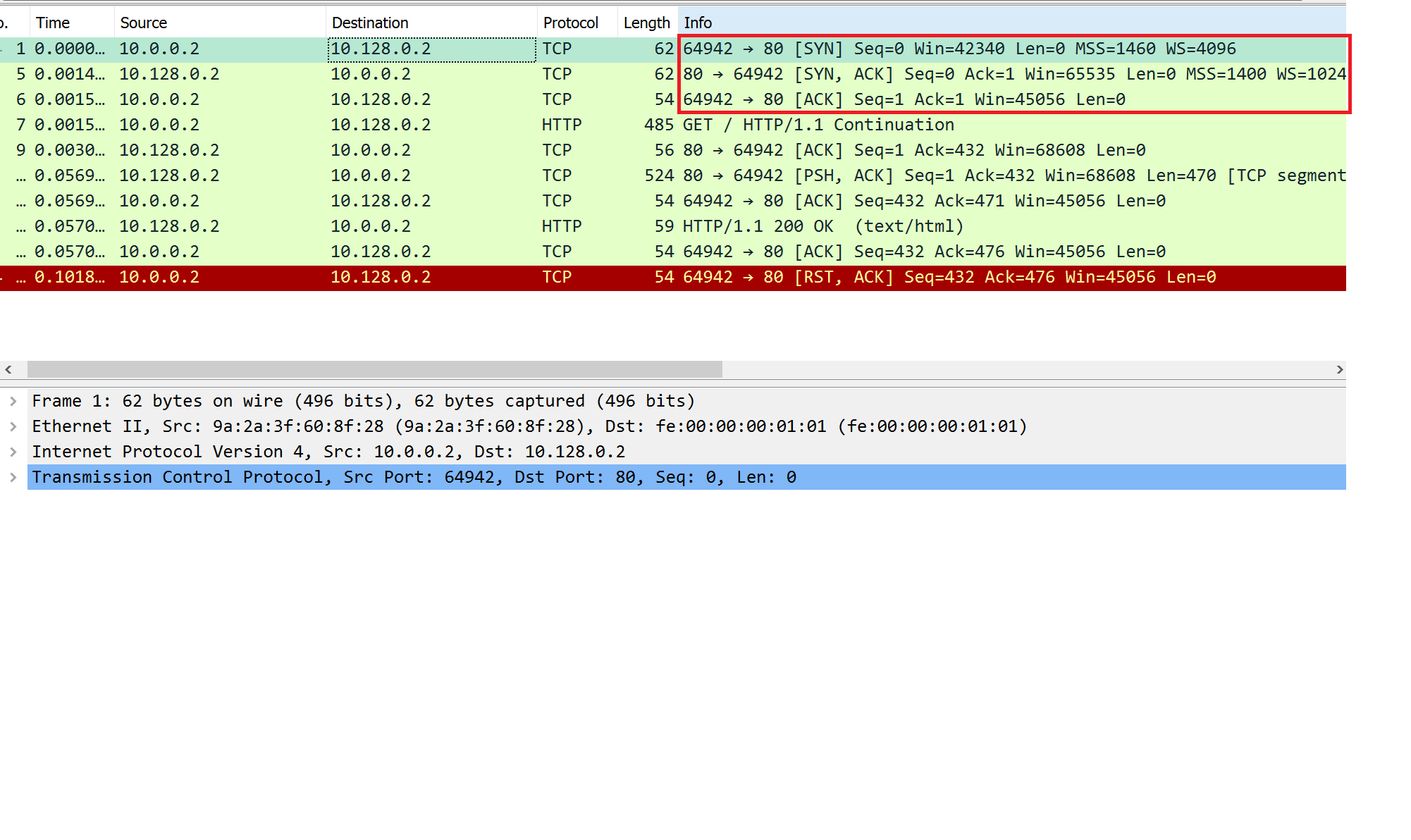
As seen in Image 1 HTTP/S MHDDOS GET, like any other HTTP Flood, starts with a standard TCP handshake.
“Image 1 – TCP Handshake”
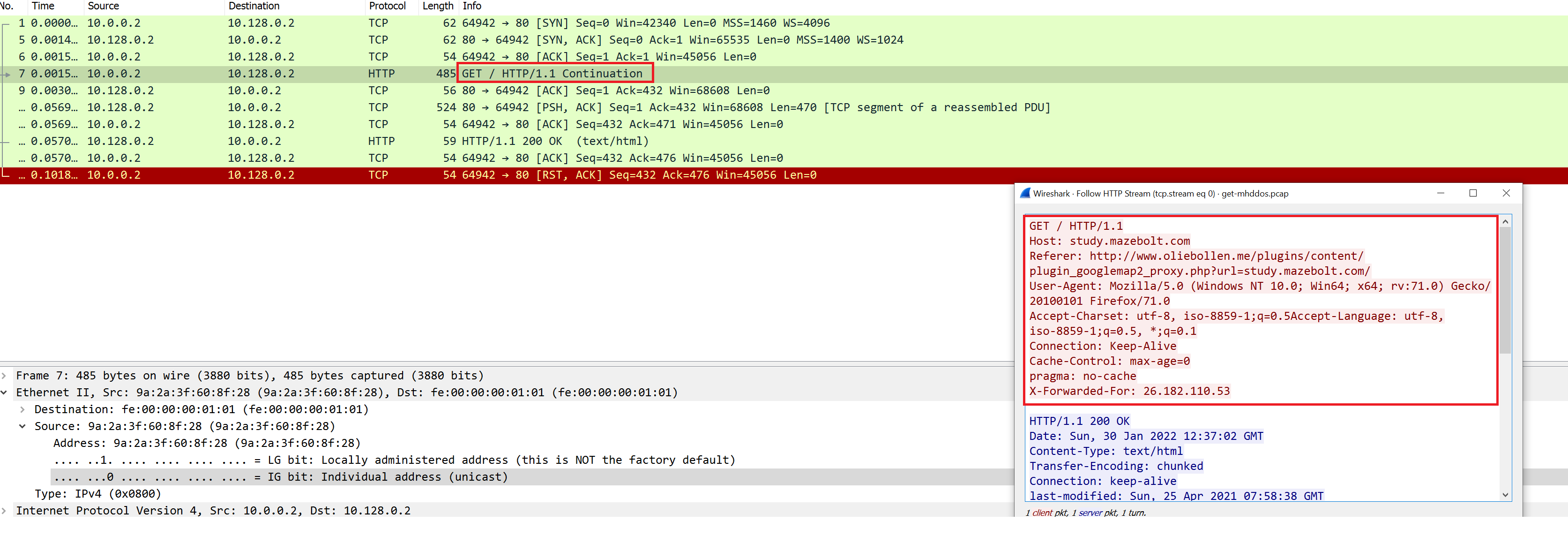
As seen in Image 2, an HTTP GET request is sent.
“Image 2 – GET Request”
HTTP/S MHDDOS GET can also be used to attack sites with HTTPS, which will then include an SSL handshake.
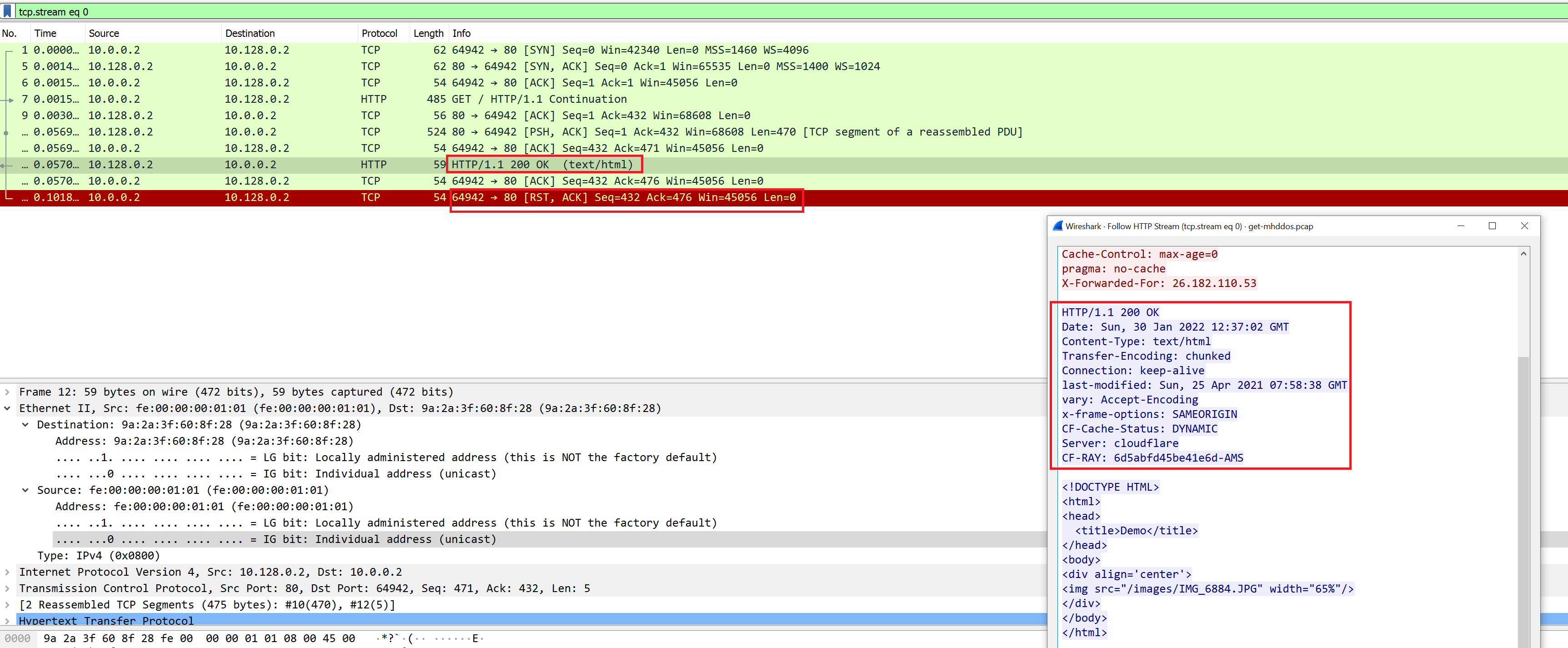
Image 3 shows a whole TCP connection cycle: packets 1-5-6 (SYN -> SYN-ACK -> ACK) establish the connection, then HTTP GET is sent from the agent, the victim responds with HTTP 200 OK (please notice the length of the packets) and then the connection is closed (RST-ACK).
“Image 3 – TCP Connection cycle including HTTP request and response”
As seen in Image 4 the capture analyzed is 9 seconds long, and the average number of packets per second are at 196. The rate is around 0.23MBit/sec. Attack rates could be much higher.
“Image 4 – HTTP/S MHDDOS GET Stats”

A typical HTTP/S MHDDOS GET running against an unsuspecting host will look similar to the above analysis. The statistics includes smaller packets of TCP handshake and larger packets of HTTP requests.
Analysis of HTTP/S MHDDOS GET in Wireshark – Filters:
Using the ‘http’ filter, you can filter out anything except HTTP requests. If a single IP address is seen as the source of multiple such requests, it might be an attacker.
“http.request.method == GET” Will show HTTP GET requests.
Download Example PCAP of HTTP/S MHDDOS GET:
*Note: IP’s have been randomized to ensure privacy.
Download