An URG-ACK-PSH flood is a DDoS attack designed to disrupt network activity by saturating bandwidth and resources on stateful devices in its path.
By continuously sending URG-ACK-PSH packets towards a target, stateful defenses can go down (In some cases into a fail open mode). This flood could also be used as a smoke screen for more advanced attacks. This is true for other out of state floods too.
URG-ACK-PSH Packets are considered an illegal packet by the Original TCP RFC. While it left room for customized behavior it is virtually unused today. Thus different systems can react differently to these packets and may cause unexpected issues and behavior.
Technical Analysis
Below an analysis of an URG-ACK-PSH flood is shown. The following images depict a high rate of URG-ACK-PSH packets being sent from a single source IP towards a single destination IP.
In Image 1 below, you can see the flood of URG-ACK-PSH packets coming from a single source. Notice the rate at which the packets are sent.
“Image 1 – example of single URG-ACK-PSH packet being sent to port 80”
In Image 2 you can see the victim responding with an RST packet. The reason this RST packet is received in response to the original URG-ACK-PSH packet is because the TCP stack receiving the URG-ACK-PSH packet never had a corresponding sequence of SYN – SYN+ACK +ACK (Otherwise known as the TCP handshake). Some environments may opt not to send a RST packet back to the source of the offending URG-ACK-PSH packet. The URG-ACK-PSH packet is known as an out of state packet.
“Image 2 – RST packet received because of “out of state” URG-ACK-PSH packet sent”
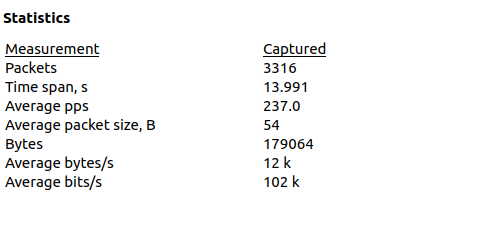
As seen in Image 3. The capture analyzed is 14 seconds long and the average number of packets per second are at 237, with a rate of around 102Kbps. These stats include returning RST packets. Attack rates could be much higher.
“Image 3 – URG-ACK-PSH Flood stats”
A typical URG-ACK-PSH flood running against an unsuspecting host will look similar to the above analysis. Generally what is seen is a high rate of URG-ACK-PSH packets (not preceded by a TCP handshake) and a slightly lesser rate of RST packets coming from the targeted server.
Analysis of an URG-ACK-PSH flood in Wireshark – Filters
Filter URG-ACK-PSH packets – “tcp.flags.urg && tcp.flags.ack && tcp.flags.push”.
Goto Statistics -> Summary on the menu bar to understand the rate you are looking at.
Download Example PCAP of URG-ACK-PSH Flood
*Note: IP’s have been randomized to ensure privacy.