Slowloris is a layer 7 DDoS attack that targets web servers and applications.
Layer 7 is the application layer of the OSI model. The HTTP protocol – is an Internet protocol that is the basis of browser-based Internet requests, and is commonly used to send form contents over the Internet or to load web pages.
Slowloris is a ‘low and slow’ DDoS attack vector. The idea with the Slowloris attack is to saturate the entire TCP stack for the HTTP/S daemon; this is done by slowly opening up connections and then sending an incomplete request in an attempt to keep the connection alive as long as possible. The tool does this slowly, and it is possible in some cases that a single attacking machine can take down a web server.
When the limit of concurrent connections is reached on the attacked server, the server can no longer respond to legitimate requests from other users, effectively causing a denial of service.
The Slowloris attack aims to fill up the connections table, making it unavailable to serve new legitimate requests from legitimate users.
This is accomplished through the use of two primary functionalities:
1. Unstable new connections opening rate – new TCP connections are requested bursty while waiting some time between each burst, making it difficult to be detected by rate-based mitigations
2. Maintain newly established TCP connections – newly established TCP connections are maintained by sending partial data through multiple HTTP requests using the same TCP connection. Forcing the target to keep the connections open while consuming connections table space and memory usage.
A constantly growing number of open connection from an attacking machine (keeping those connections alive) can be considered as a high probability sign of the Slowloris attack.
Technical analysis
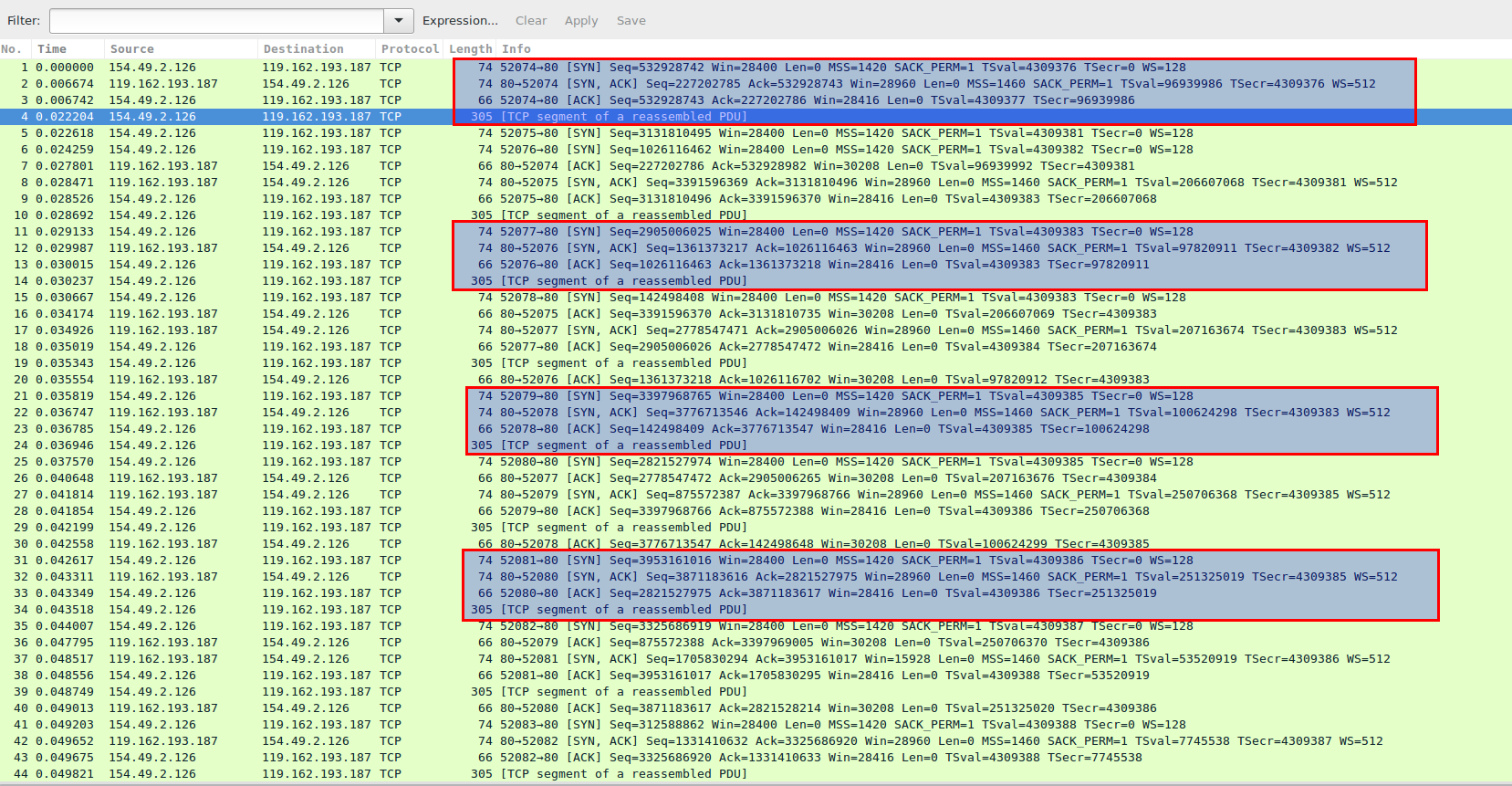
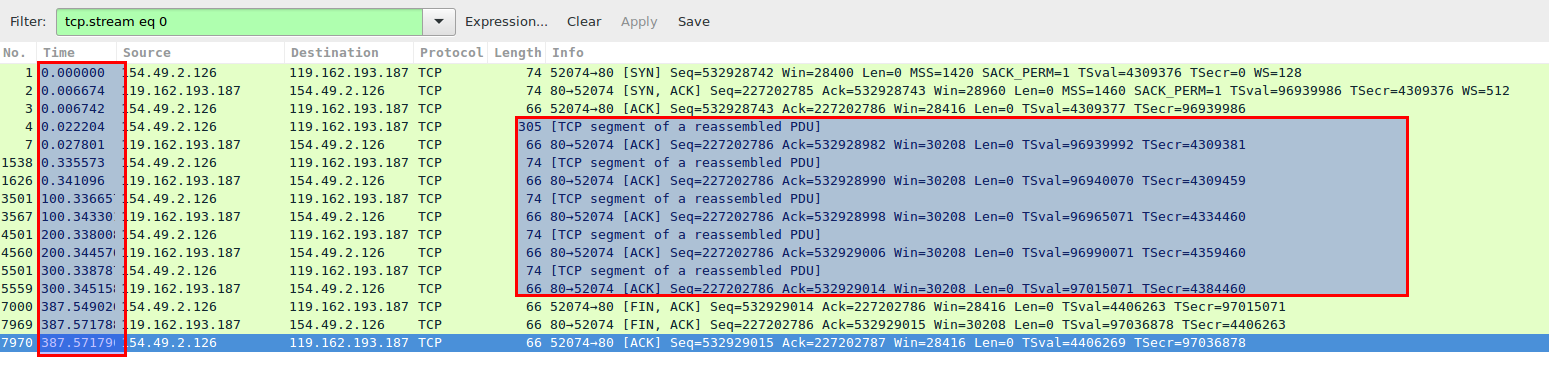
In image 1 you can see “client” establishes TCP connections and sends initial incomplete packages to keep the connection alive.
Image 1 – establishing TCP connection and “marking” it alive.
Client establishes TCP connection to the server using 3-Way Handshake (SYN, SYN-ACK, ACK) – packets 1,2,3 and then sends a “keep-alive signal” – packet 4. Single client will aim to establish as many such connections as possible, but not to go over detection threshold.
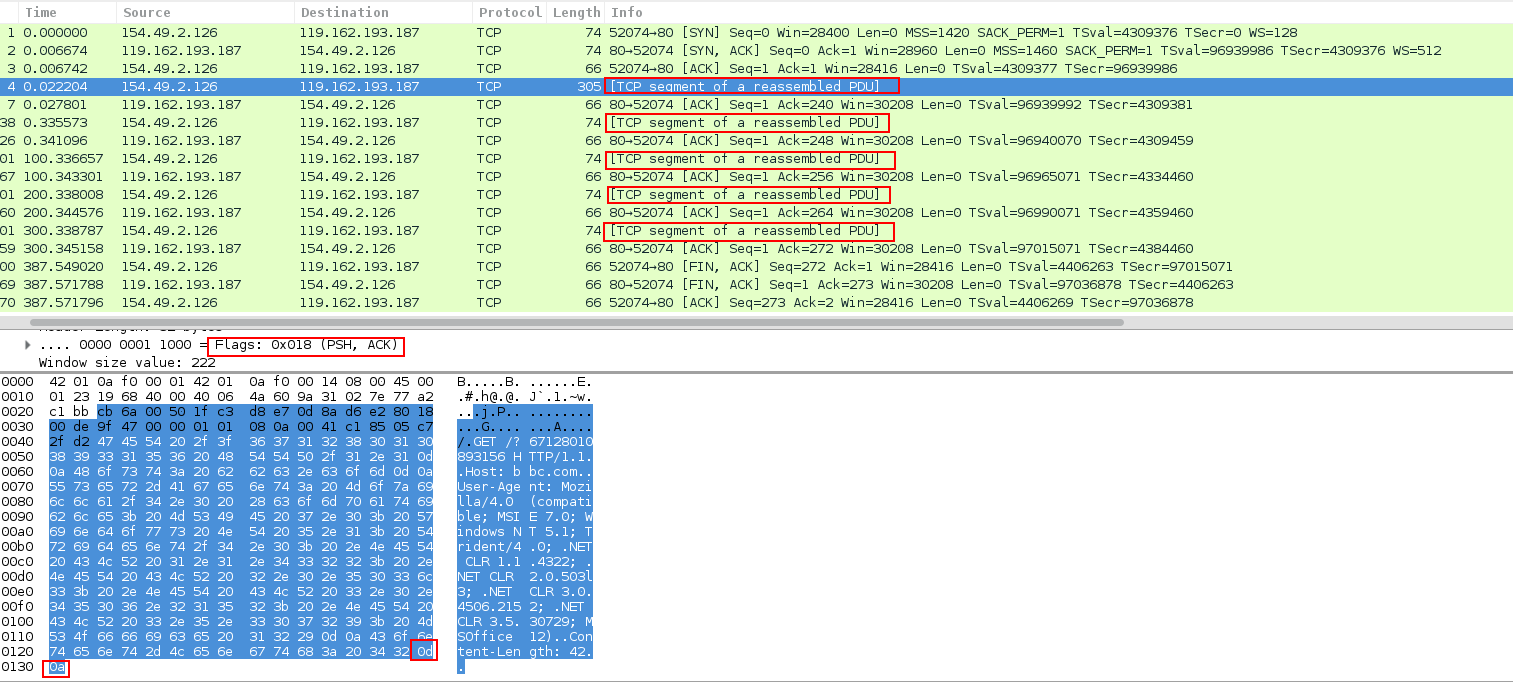
Image 2 shows 5 “keep alive” packets have been sent during a single TCP connection.
Image 2 – keeping established connections alive and opening new ones
“Keep alive” packets contain PSH ACK Flags and have incomplete HTTP header. Notice that it is missing one CRLF to finish the header which is otherwise completely legitimate.
The HTTP protocol specification (RFC 2616) states that a blank line must be used to indicate the end of the request headers and the beginning of the payload, if any. Once the entire request is received, the web server may then respond. But in our case the header ends with “0d0a” in HEX (“.”), while a complete header should end with “0d0a0d0a” (“..”)
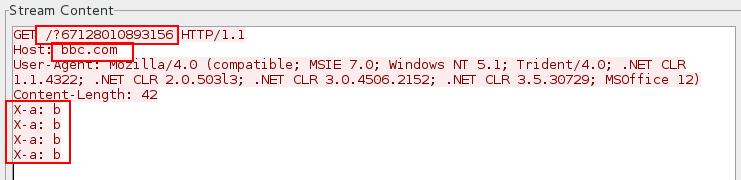
Image 3 shows HTTP Header with randomized URL (/?671280108…) and host (bbc.com). HTTP Request is not complete and it is partial. The bogus header line the tools sends is currently:
X-a: b
Which obviously doesn’t mean anything to the server so it keeps waiting for the rest of the header to arrive. The same bogus header is resent in all 5 “keep alive” packets.
Image 3 – HTTP Header of “keep alive” packets
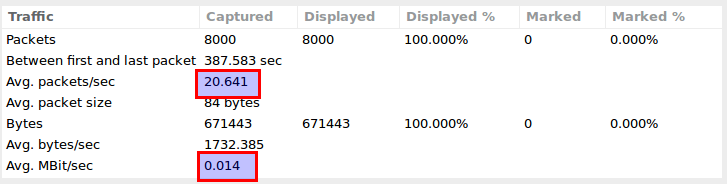
Image 4 displays that the capture analyzed is more than 6 minutes long and the average number of packets per second are at 20.6, with a rate of around 0.014MBit/sec. Attack rates could be much higher.
Image 4 – HTTP/S Slowloris traffic stats
The above stats are show for a single attacker node. But, even for a massive Slowloris attack the stats per attacker will look very similar. The analyzed capture represents a more than 6 minutes of attack traffic. And, as one can see the stats are more than modest.
Analysis of HTTP/S Slowloris in WireShark
There is no specific filter one can apply to make the Slowloris to stand out. Analysis is done by applying ip.addr == ‘suspected_attacker’ and following TCP streams.
Possible indicators are:
– numerous tcp-handshakes followed by TCP segmented packets only
– absence of meaningful data packets
– resending of same incomplete HTTP headers
– absence of FIN packets. The figure shows FIN packets, because the attack was explicitly stopped for this example having a complete TCP stream.