HTTP OPTIONS flood is a layer 7 DDoS attack that targets web servers and applications.
Layer 7 is the application layer of the OSI model. The HTTP protocol – is an Internet protocol which is the basis of browser-based Internet requests, and is commonly used to send form contents over the Internet or to load web pages.
HTTP OPTIONS floods are designed to overwhelm web servers’ resources by continuously requesting single or multiple URL’s from many sources attacking machines, which simulate an HTTP clients, such as web browsers (Though the attack analyzed here, does not use browser emulation).
An HTTP OPTIONS Flood consists of OPTIONS requests. Unlike other HTTP floods that may include other request methods such as POST, PUT, GET, etc.
When the server’s limits of concurrent connections are reached, the server can no longer respond to legitimate requests from other clients attempting to OPTIONS, causing a denial of service.
HTTP OPTIONS flood attacks use standard URL requests, hence it may be quite challenging to differentiate from valid traffic. Traditional rate-based volumetric detection is ineffective in detecting HTTP OPTIONS flood attacks since traffic volume in HTTP OPTIONS floods is often under detection thresholds. However, HTTP OPTIONS flood uses the less common OPTIONS method. As such, it may be beneficial to review network traffic carefully when witnessing many such incoming requests.
Technical analysis
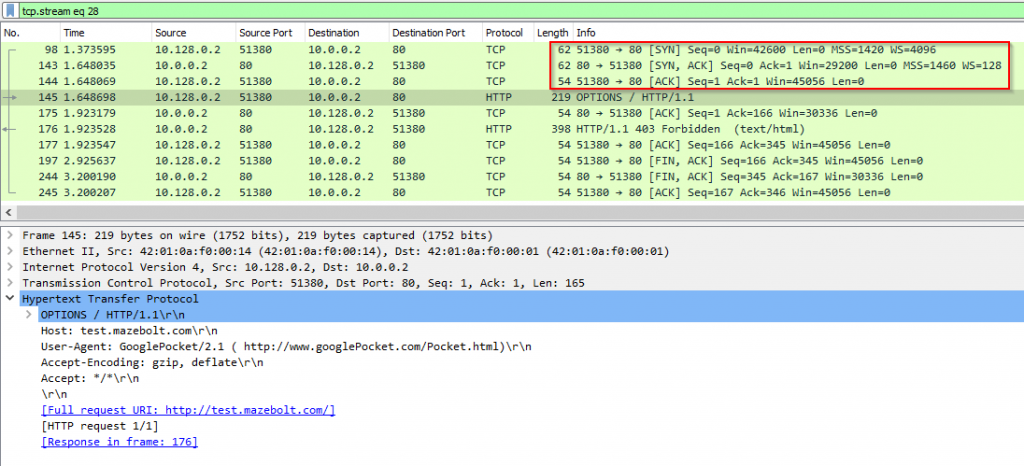
To send an HTTP OPTIONS request client establishes a TCP connection. Before sending an HTTP OPTIONS request a TCP connection between a client and a server is established, using 3-Way Handshake (SYN, SYN-ACK, ACK), seen in packets 98,143,144 in Image 1. The HTTP request will be in a PSH, ACK packet.
Image 1 – Example of TCP connection
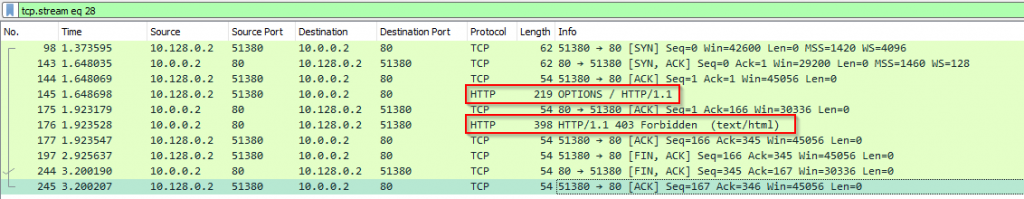
An attacker (IP 10.128.0.2) sends HTTP/1.1 OPTIONS requests, while the target responds with HTTP/1.1 403 Forbidden as seen in Image 2.
While in this flow we see an HTTP/1.1 403 Forbidden, that might change depending on the web server settings.
Image 2 – Example of HTTP packets exchange between an attacker and a target:
The capture analyzed is around 3.5 seconds long while it contains an average of 80 PPS (packets per second), with an average traffic rate of 0.07 Mbps (considered low, the attack you are analyzing could be significantly higher).
Image 3 – HTTP Flood stats

Analysis of HTTP OPTIONS Flood in WireShark – Filters
“http” filter – Will show all http related packets.
“http.request.method == OPTIONS” – Will show HTTP OPTIONS requests.
It will be important to review the user agent and other HTTP header structures as well as the timing of each request to understand the attack underway.
Download example PCAP of HTTP OPTIONS Flood attack
*Note: IP’s have been randomized to ensure privacy.
Download